From work made for hire to intellectual property and trade secrets, your program must ensure contingents are part of the risk mitigation efforts.
An often-overlooked area of risk in most CW engagements is the protection of the work produced by contingent workers during the engagement and under the agreement the engagement is operating under. That, along with intellectual property and a company’s trade secrets, requires a careful and well-considered approach.
Work for Hire
Work for hire is an exception to the general rule that the person who creates a work is the legally recognized author of that work. According to copyright law and certain other copyright jurisdictions, if a work is “made for hire,” the employer is considered the legal author/owner.
In the context of contingent work, a work made for hire is a work subject to copyright that is created by a contingent worker as part of their service engagement that all parties agree to in writing as a “work for hire (WFH)” designation.
Trade Secret
Technical or nontechnical data, a formula, pattern, compilation, program, device, method, technique, or process that derives independent economic value, actual or potential, from not being generally known to, and not being readily ascertainable by proper means by other persons who can obtain economic value from its disclosure or use. Additionally, a trade secret must actually be a secret or subject to “reasonable efforts” to be kept a secret.
Concerns around the ownership of work can be mitigated with the inclusion of a work-for-hire clause in the contingent worker’s agreement. While the law protects “work for hire” [see box], work product protection clarifies ownership of items delivered under a contingent engagement agreement.
However, depending on which state your contingent worker is operating in and whether the work is copyrightable and patentable, you may need to have additional documents signed directly by the worker. Also, in many circumstances, a work-for-hire agreement is not enforceable if the worker does not sign it directly; the staffing partner’s signature can be of limited to no value.
Meanwhile, just as with their in-house employees, companies must consider their contingent workforce in their intellectual property and their trade secrets protection plans. This work can get complicated, especially with the regulations and statutes governing IP and trade secret protections that vary from state to state. But it can become fairly manageable if you inventory what information you need to protect and then take appropriate and reasonable steps to protect it. So, what might be considered a best practice approach to managing the protection of work product/IP?
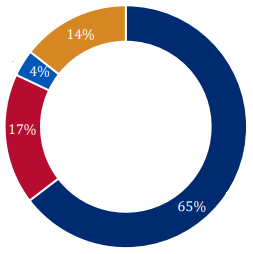
Inventory. First, inventory what you are trying to protect. Identify your key IP and trade secrets and manage them accordingly. For example, customer information (price, cost, margin, purchasing history) ranks among the most stolen categories of IP from organizations, while trade secrets often at risk are technical or scientific information or formulas and methods for making products. This IP is certainly very important, but critical IP/trade secrets are more than technical and/or scientific materials. Other types of IP data can have tremendous economic value if stolen from an organization.
Working details. Second, as noted earlier, executing contractual clauses is fundamental, but so is the location of the service engagement being executed and understanding how those agreements align with the state statutes where most IP protection governance and rules are defined/determined.
Finally, execute key IP protection policies with incoming and outgoing talent — whether CW or full-time employees — ranging from training incoming talent not to bring any protected IP from previous employers to executing a calendared IP preservation protocol with current employees who will at some point exit the organization for another employer or through retirement.
Once you have your IP protection protocol in place with CW contract clauses and nondisclosure agreements, proper execution of invention assignment tools when appropriate, and an organized and reasonable effort to keep important company IP secret and/or confidential, you can then track your protocol’s performance, make adjustments when needed and start worrying about your next CW risk program opportunity and challenge.